What is Azure Key vault? - Part 1
- Pre-requisite Knowledge –
Before you understand the Azure key vault, I recommend you should know –
- Basic knowledge of software implementation
- Basic knowledge of Microsoft Azure and pillars of Azure cloud
- Background –
In my previous articles, we have seen an overview of Azure, BLOB storage, IoT, Azure backup, storage, Web Jobs, KUDU, etc.
Now, we will learn a more secure way mechanism by one feature from Microsoft Azure services i.e. what is Azure key vault.
- Azure Key vault
Traditionally, for encryption of business-critical data protection and compliance purpose software secrets on which application logic runs like connection string, passwords, secrets keys, PFX files, API keys, etc. are stored using couple of ways like storing it in configuration files like web.config, encrypt this information and use it in business logic by decrypting it.
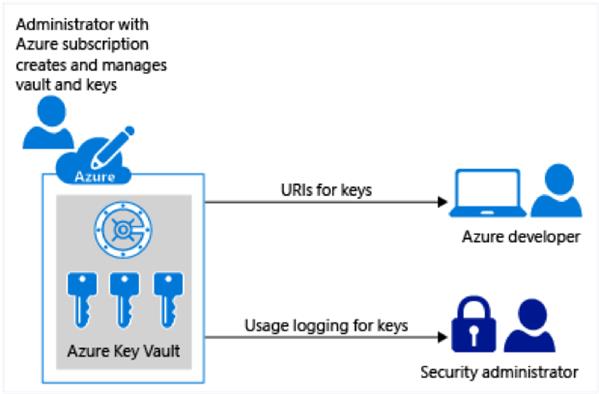
Microsoft Azure has one service to secure your small secret information like passwords or other secrets by using Azure key vault and developers no longer need to use this information in the application code level or neither in application configuration level. This is very secure since application or even Microsoft has no direct access to this information. Only users can grant permission to access it or use it. The development team can use the encryption keys to encrypt the data and store it into Azure key vault. Even, we can manage Secure Sockets Layer/Transport Layer Security (SSL/TLS) certificates by using this service. Azure key vault information is secured in various ways like software or FIPS 140-2 Level 2 validates hardware security modules. Authorized users can create, import, encrypt, decrypt the encryption keys quickly in a minute.
It has a key-value pair. We can create and manage this information by using the Azure portal. The information of the Azure key vault can be accessed using the URI. Access to a key vault requires proper authentication and authorization before a caller (user or application) can get access. If we use the Azure key vault feature, then we can manage the secrets centrally at one place in the most secure way.
Authentication with Azure key vault is done by Azure active directory and authorization can be done by using role-based access (RBAC) security mechanism. Azure key vault can be monitored with the logs information and it needs to be enabled.
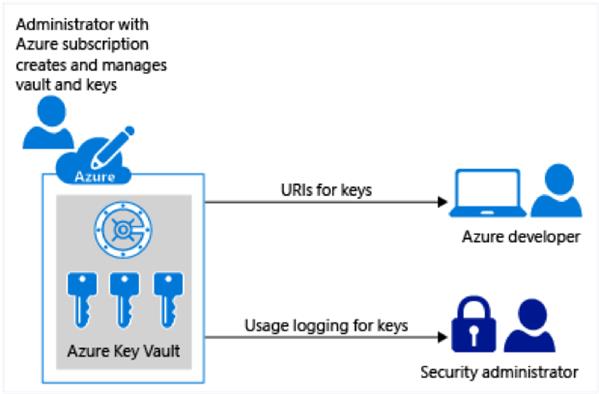
Image Source – Microsoft Docs
It is recommended to use this feature for –
- To store business-critical secrets like certificates, connection strings, and passwords, etc.
- Use Azure key vault per application per environment. This helps to not share the keys between environments.
- Make sure to regularly backup the Azure key vault.
- Set an alert and enable the logging of it.
- Turn on the recovery option.
Azure Key Vault Documentation – Refer this page
Conclusion - In this article, we have learned Azure application security using Azure key vault service. In the next article, we will learn Azure key vault terms and how it works internally.
I will keep writing, stay tuned!